Firepower Variable Sets
Last Updated: [last-modified] (UTC)
Below is an example of a SNORT rule. This particular rule looks for a Trojan called Cryptowall.
Notice that the first line has the values $HOME_NET and $EXTERNAL_NET? These are variables. SNORT uses these variables to represent the protected and the unprotected networks.
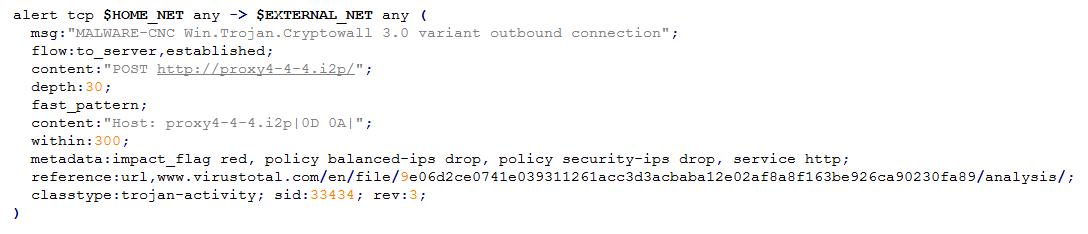
Variables are useful, as values can be set or changed in a global area. This means that there is no need to edit individual SNORT rules. In Firepower, a global list of variables is a Variable Set.
FMC comes with a default variable set. It’s HIGHLY RECOMMENDED to change these values to represent your network. You should create your own set and change that, rather than modifying the default set.
Customising Variable Sets
Variables Cheat Sheet
There are many variables in FMC. Below is a table of the common variables that you should consider changing. If nothing else, change the $HOME_NET variable.
You can use objects and object groups to make future changes simple.
| Variable | Usage | Default Value | Notes |
|---|---|---|---|
| $HOME_NET | Specifies the protected network | any | Add trusted networks in here |
| $EXTERNAL_NET | Specifies the outside network | any | Add $HOME_NET as an exclusion here |
| $SIP_SERVERS | Define SIP servers | HOME_NET | A list of IP’s |
| $SMTP_SERVERS | Define SMTP servers | HOME_NET | A list of IP’s |
| $SNMP_SERVERS | Define SNMP servers | HOME_NET | A list of IP’s |
| $SQL_SERVERS | Define SQL servers | HOME_NET | A list of IP’s |
| $SSH_SERVERS | Define SSH servers | HOME_NET | A list of IP’s |
| $TELNET_SERVERS | Define telnet servers | HOME_NET | A list of IP’s |
| $FTP_PORTS | Ports that FTP runs on | 21, 2100, 3535 | Only change if non-default ports are needed |
| $HTTP_PORTS | Ports that HTTP runs on | Many ports | Only change if non-default ports are needed |
| $ORACLE_PORTS | Ports that Oracle databases run on | any | Only change if non-default ports are needed |
| $SSH_PORTS | Ports that are used for SSH | 22 | Only change if non-default ports are needed |
Creating a Variable Set
Variable sets are objects, which are in Objects -> Object Management -> Variable Set.
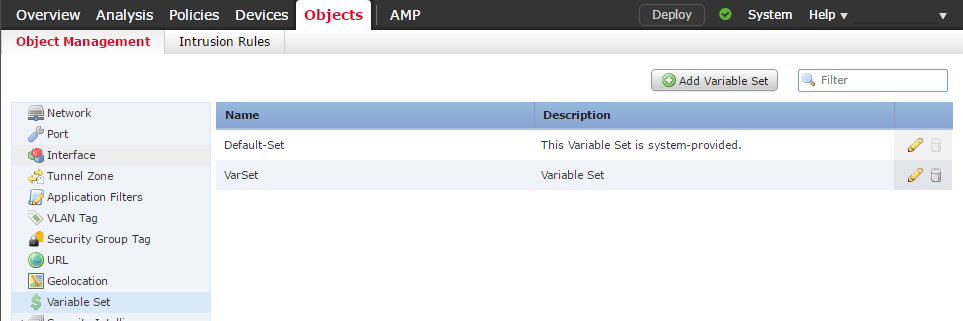
The Default-Set object is available out of the box. Create a new variable set by clicking the Add Variable Set button.
The new set will use the values in the default set as a starting point. This is why it’s a good idea to use custom sets, and leave the default as it is.
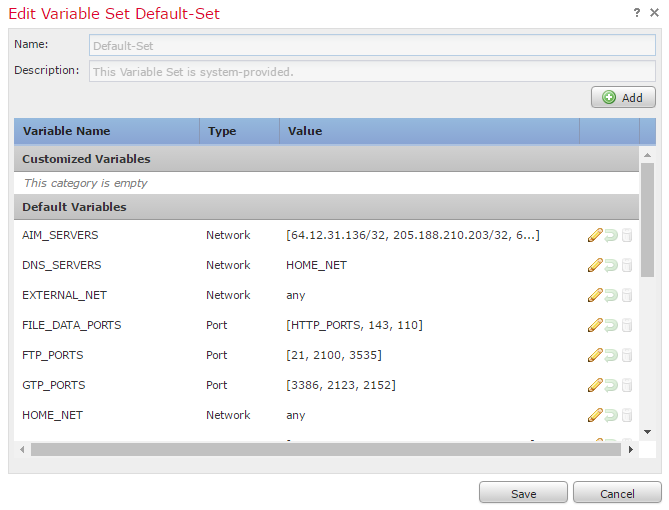
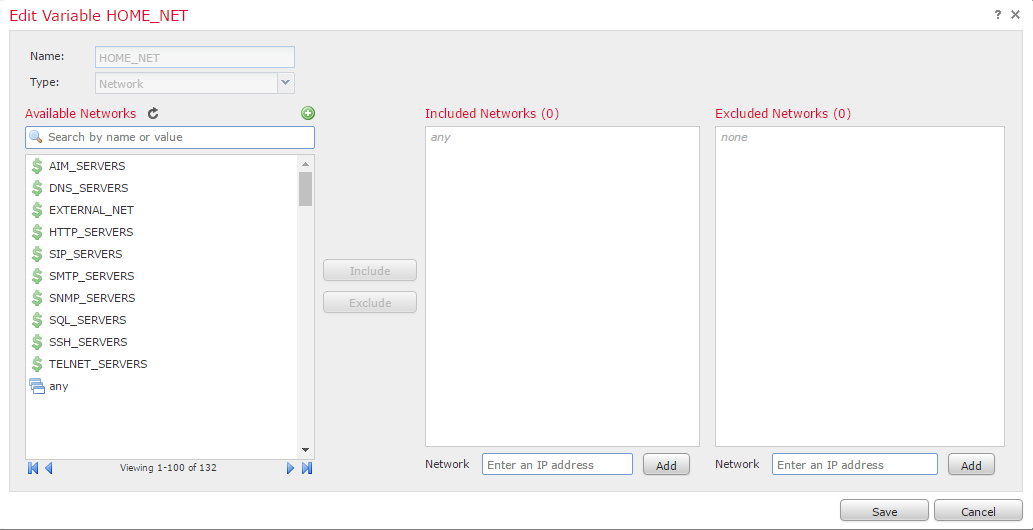
Here you can see a list of every variable. Variables are system-wide. When you create a new variable, it is available in every variable set. The value that the variable contains can be different in each set.
If you look at the HOME_NET variable, you can see that it is set to any. This is why you should edit the default variable set. The default variable set cannot distinguish between trusted and untrusted networks.
Each variable is customisable. Variables can be static values, or reusable objects.
Applying a Variable Set
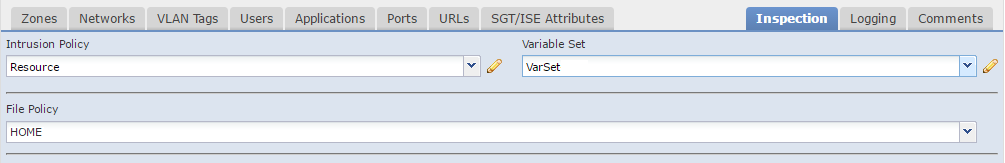
Pair variable sets with an Intrusion Policy in an Access Control Policy. This can be per rule or a default action.
References
Cisco – Reusable Objects