
Campus FHRP Tuning
Last Updated: [last-modified] (UTC)
If you use the traditional layer-2 access model in the campus, you will need to use an FHRP for redundancy. Depending on your choice of FHRP (HSRP, VRRP, or GLBP), there may be some options to tune performance.
FHRP tuning is also useful if you’re studying for the CCDP ARCH exam.
Before proceeding, it is recommended to understand the Layer-2 Multi-Tier Design
[maxbutton id=”4″ text=”Hierarchy Design” url=”https://networkdirection.net/Hierarchy+Design+Part+1″]
FHRPs in the Distribution Layer
The FHRP should be in the distribution layer. If you’re fortunate enough to be using the VSS model or routed access model, you don’t need an FHRP at all.In this model, the best convergence possible is 800ms. This is due to the hellos and hold-down timers. To achieve this convergence, enable sub-second timers.
FHRP Selection
HSRP vs VRRP
 HSRP and VRRP are very similar. HSRP is Cisco’s proprietary technology, while VRRP is the industry standard.
HSRP and VRRP are very similar. HSRP is Cisco’s proprietary technology, while VRRP is the industry standard.
One very small advantage to going HSRP over VRRP is that Cisco can innovate with HSRP. Improvements to VRRP take longer, as they have to pass through the standards body.
Some people like to point out that VRRP is better, as it will work in a mixed-vendor environment. While this is true, an FHRP is usually used with a pair of matched switches. How often do you deploy a switch pair, where each switch is from a different vendor?
A real advantage to VRRP is that it doesn’t use a separate VIP like HSRP does. From this perspective, IP management is a little simpler.
There is no true load-sharing across both routers with either HSRP or VRRP. This can be achieved with workarounds. One option is to make one router active for all even VLANs and make the other active for all odd VLANs. Another option is to create two different FHRP groups. DHCP hands out both IP’s as a default gateway, in a round-robin fashion.
Both VRRP and HSRP support plain text and MD5 authentication.
GLBP
GLBP is another of Cisco’s FHRP’s, which they support on some of their platforms. It is capable of running in active/active mode.
One possible issue this causes is asymmetric routing. Traffic may route out of Switch-A, and return on Switch-B. This may not be a problem often, but imagine if there are inline security devices, such as an IPS. They will not see the entire conversation, which may cause them to block traffic, or allow bad traffic. In a case like this, consider HSRP or VRRP.
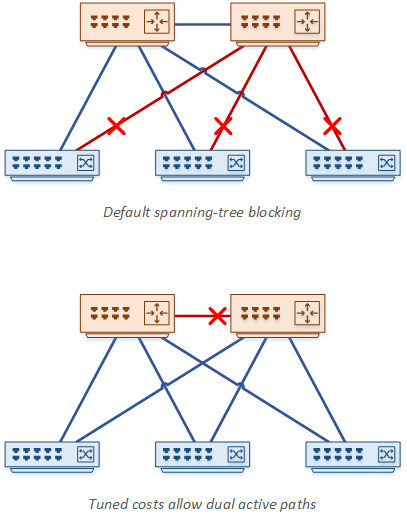
There is another possible issue between the access and distribution layers. As shown below, spanning-tree will likely block links to the access layer switches. One of the distribution switches will not be able to forward traffic. This neutralises the benefits of GSLB active/active.
The workaround is to change the port cost on the layer-2 distribution link. This link is now blocked, rather than the access layer links. An alternative is to use a model with a routed link between the distribution switches.
GLBP support both plain text and MD5 authentication.
Preemption
 HSRP and VRRP may use preemption. This is where one switch or router can take over the active role after it starts up.
HSRP and VRRP may use preemption. This is where one switch or router can take over the active role after it starts up.
When spanning-tree is in the network, it is important to align the HSRP active switch with the root bridge. To add to this, use preemption. If a switch reboots, and becomes the root bridge after startup, it will also take over the active FHRP role.
When configuring preemption, add a delay time. When a switch boots, it needs time to learn routes from the network and to build its routing table. If it becomes the active switch straight away, there may be traffic loss until the routing table is ready.
The recommended preemption delay value is the boot time of the switch, plus 50%.
References
Cisco Live – BRKCRS-2031 – Enterprise Campus Design: Multilayer Architectures and Design Principles
Cisco – Campus Network for High Availability Design Guide
Cisco – Configuring VRRP
Cisco – HSRP MD5 Authentication
Cisco – Configuring GLBP
Marwan Al-shawi and Andre Laurent – Designing for Cisco Network Service Architectures (ARCH) Foundation Learning Guide: CCDP ARCH 300-320 (ISBN 158714462X)